In today's rapidly evolving digital landscape, businesses of all sizes rely heavily on technology to...


In today's rapidly evolving digital landscape, businesses of all sizes rely heavily on technology to...
Organizations rely on the security that cyber insurance offers as the frequency and severity of cyberattacks...

11 Key Reasons to Choose a Reputable IT Provider. In today's fast-paced and digitally driven business...

Photo by Luca Bravo on Unsplash In today's competitive business landscape, employee productivity is a...

Philantech3 recognizes the importance of an effective security program to protect our clients and the...
How often should company PCs be replaced?This is a common question from our clients. As you might expect,...
Email security is a crucial concern for all businesses, regardless of size. Protecting sensitive information...

On Dec. 2nd, 2022, Rackspace (an enormous Infrastructure as a Service hosting company) experienced an outage...

This is a guest post, written by Nicola Reid of Business 4 Today. In today's business world, it's more...

Let’s start with the definition of vulnerability in cybersecurity. Essentially, a vulnerability is a...

The Top Cyber Security Threats Facing Enterprises and How to Mitigate Them As cybersecurity threats become...

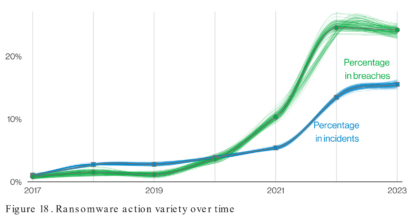
2022 Computer Security Review Reports of company network breaches have increased steadily due to massive...