

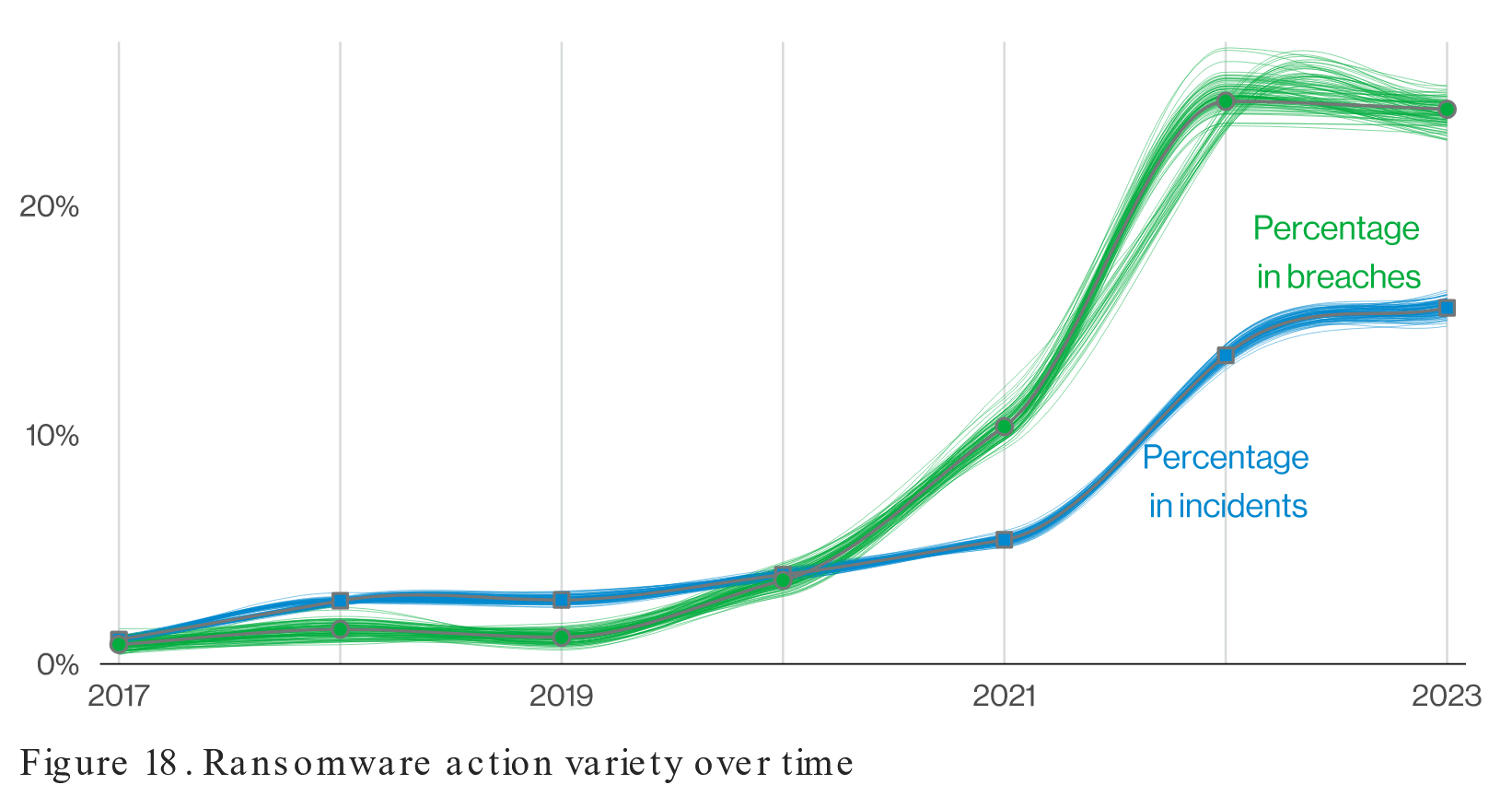
Having Trouble Renewing Your Cyber Insurance Policy?
Organizations rely on the security that cyber insurance offers as the frequency and severity of cyberattacks rise. In the event of a successful breach or ransomware attack, the appropriate policy will minimize responsibility and keep damages in check. Until recently,...
Optimizing Business Processes with Microsoft
11 Key Reasons to Choose a Reputable IT Provider. In today’s fast-paced and digitally driven business landscape, staying competitive and efficient is paramount. One of the most effective ways to achieve this is by optimizing your business processes through the...
10 Strategies to Boost Employee Productivity & Company Success
Photo by Luca Bravo on Unsplash In today’s competitive business landscape, employee productivity is a critical factor for the success of any organization. Productive employees not only contribute to higher efficiency and profitability but also foster a positive...
Security Commitment & Privacy Policy
Philantech3 recognizes the importance of an effective security program to protect our clients and the company’s employees, assets, information, integrity and reputation from potential threats. Additionally, Philantech3 respects the privacy rights of all individuals,...
Company PCs (Should You Replace Them?)
How often should company PCs be replaced?This is a common question from our clients. As you might expect, there are a range of opinions and policies on this topic. Some adopt the strategy of using a PC until it fails or shows signs of failure. This is very...
Email Security (Do You Use Two-Factor Authentication?)
Email security is a crucial concern for all businesses, regardless of size. Protecting sensitive information such as login credentials, customer data, and confidential documents is essential to avoid data breaches and cyber-attacks. One of the most effective ways to...
Security Incident: What Can You Do To Prepare?
On Dec. 2nd, 2022, Rackspace (an enormous Infrastructure as a Service hosting company) experienced an outage on their Hosted Microsoft Exchange (HEX) service, leaving ALL HEX customers without access to email. The next day, Rackspace announced that it was a security...
Tech Innovations Every Small Business Should Know About
This is a guest post, written by Nicola Reid of Business 4 Today. In today’s business world, it’s more important than ever to have a strong presence both in the real world and online. Luckily, there are a number of ways that small businesses can use...

Recent Comments